A development lab used by Samsung engineers was leaking highly sensitive source code, credentials and secret keys for several internal projects — including its SmartThings platform, a security researcher found.
The electronics giant left dozens of internal coding projects on a GitLab instance hosted on a Samsung-owned domain, Vandev Lab. The instance, used by staff to share and contribute code to various Samsung apps, services and projects, was spilling data because the projects were set to “public” and not properly protected with a password, allowing anyone to look inside at each project, access, and download the source code.
Mossab Hussein, a security researcher at Dubai-based cybersecurity firm SpiderSilk who discovered the exposed files, said one project contained credentials that allowed access to the entire AWS account that was being used, including over a hundred S3 storage buckets that contained logs and analytics data.
Many of the folders, he said, contained logs and analytics data for Samsung’s SmartThings and Bixby services, but also several employees’ exposed private GitLab tokens stored in plaintext, which allowed him to gain additional access from 42 public projects to 135 projects, including many private projects.
Samsung told him some of the files were for testing but Hussein challenged the claim, saying source code found in the GitLab repository contained the same code as the Android app, published in Google Play on April 10.
The app, which has since been updated, has more than 100 million installs to date.
“I had the private token of a user who had full access to all 135 projects on that GitLab,” he said, which could have allowed him to make code changes using a staffer’s own account.
Hussein shared several screenshots and a video of his findings for TechCrunch to examine and verify.
The exposed GitLab instance also contained private certificates for Samsung’s SmartThings’ iOS and Android apps.
Hussein also found several internal documents and slideshows among the exposed files.
“The real threat lies in the possibility of someone acquiring this level of access to the application source code, and injecting it with malicious code without the company knowing,” he said.
Through exposed private keys and tokens, Hussein documented a vast amount of access that if obtained by a malicious actor could have been “disastrous,” he said.
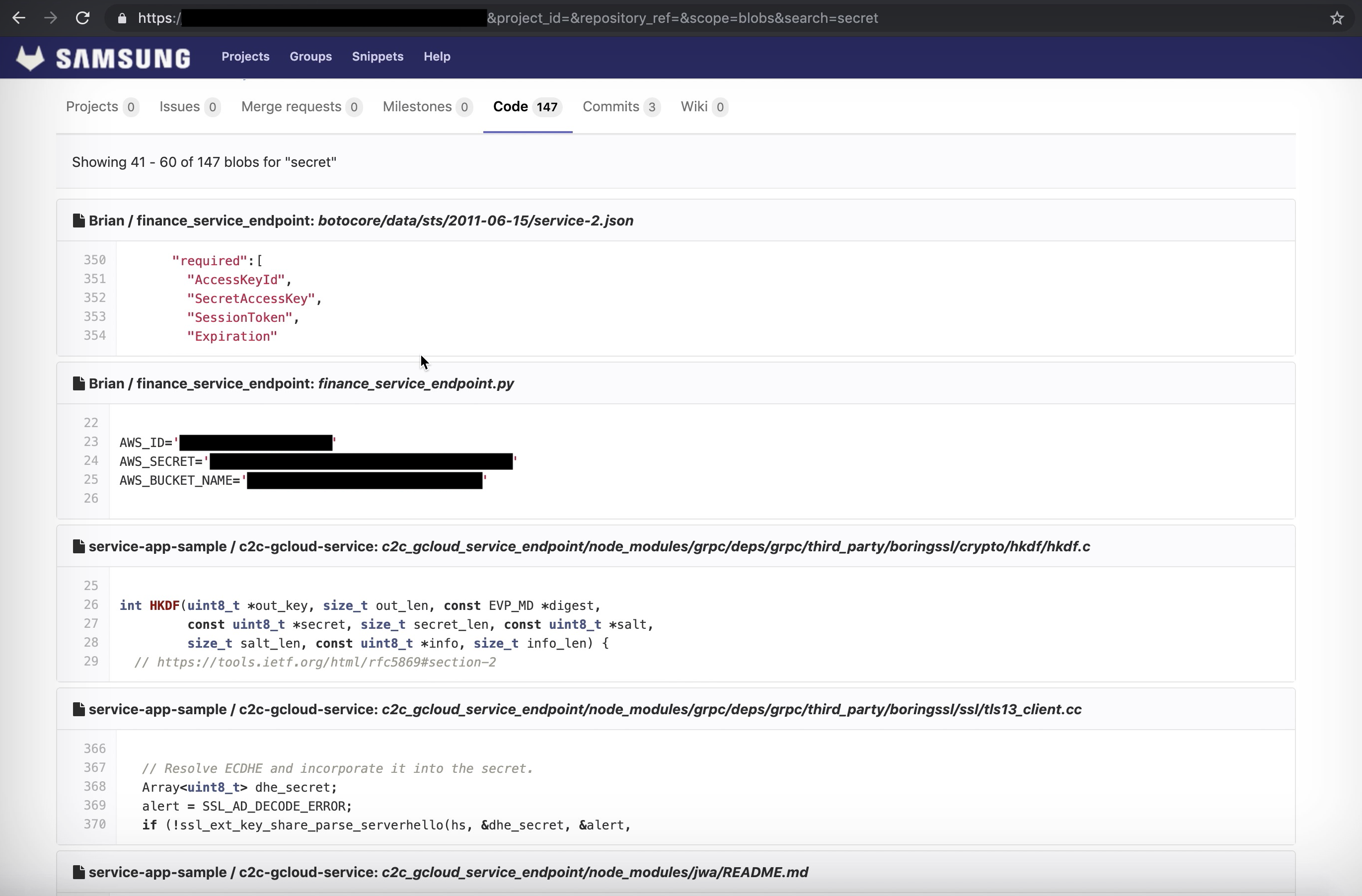
A screenshot of the exposed AWS credentials, allowing access to buckets with GitLab private tokens. (Image: supplied).
Hussein, a white-hat hacker and data breach discoverer, reported the findings to Samsung on April 10. In the days following, Samsung began revoking the AWS credentials but it’s not known if the remaining secret keys and certificates were revoked.
Samsung still hasn’t closed the case on Hussein’s vulnerability report, close to a month after he first disclosed the issue.
“Recently, an individual security researcher reported a vulnerability through our security rewards program regarding one of our testing platforms,” Samsung spokesperson Zach Dugan told TechCrunch when reached prior to publication. “We quickly revoked all keys and certificates for the reported testing platform and while we have yet to find evidence that any external access occurred, we are currently investigating this further.”
Hussein said Samsung took until April 30 to revoke the GitLab private keys. Samsung also declined to answer specific questions we had and provided no evidence that the Samsung-owned development environment was for testing.
Hussein is no stranger to reporting security vulnerabilities. He recently disclosed a vulnerable back-end database at Blind, an anonymous social networking site popular among Silicon Valley employees — and found a server leaking a rolling list of user passwords for scientific journal giant Elsevier.
Samsung’s data leak, he said, was his biggest find to date.
“I haven’t seen a company this big handle their infrastructure using weird practices like that,” he said.
Read more:
- Security lapse exposed a Chinese smart city surveillance system
- A leaky database of SMS text messages exposed password resets and two-factor codes
- Chipotle customers are saying their accounts have been hacked
- We found a massive spam operation — and sunk its server
- Dow Jones’ watchlist of 2.4 million high-risk individuals has leaked
- Stop saying, ‘We take your privacy and security seriously’
- Robocaller firm Stratics Networks exposed millions of call recordings
- Massive mortgage and loan data leak gets worse as original documents also exposed
Read Full Article
No comments:
Post a Comment